In today's complex and highly regulated world, the secure and verifiable disposal of sensitive data, confidential documents, and obsolete assets is no longer optional—it's a critical imperative. Businesses, organizations, and even individuals are increasingly faced with the challenge of proving that material has been properly destroyed, not just discarded. This is where a Destruction Certificate Template becomes an indispensable tool, providing a standardized, legally defensible record of such activities. It serves as official documentation, confirming that specific items or data have been eradicated according to defined protocols, offering peace of mind and demonstrating compliance with various legal and industry standards.
The necessity for such a certificate spans numerous industries, from healthcare providers handling patient records to financial institutions managing sensitive client information, and technology companies disposing of data storage devices. Without clear proof of destruction, entities remain vulnerable to potential data breaches, legal penalties, reputational damage, and environmental liabilities. A well-crafted destruction certificate mitigates these risks by creating an auditable trail of disposal.
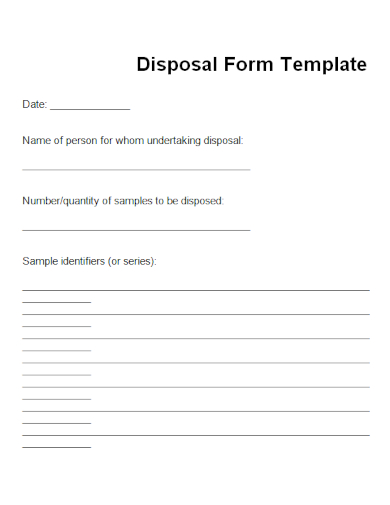
However, crafting such a document from scratch can be time-consuming and prone to omissions. This is why leveraging a robust template is highly beneficial. It ensures that all essential information is captured consistently, providing a professional and comprehensive record without the need to reinvent the wheel for every disposal event. Whether you're decommissioning IT equipment, shredding confidential papers, or permanently deleting digital files, a standardized template streamlines the process.

This article will delve into the critical role of these certificates, explore their key components, and guide you on how to effectively utilize a template to meet your specific needs. Understanding the intricacies of proper destruction documentation is vital for maintaining security, upholding privacy, and adhering to the ever-evolving landscape of regulatory compliance.

What is a Destruction Certificate?
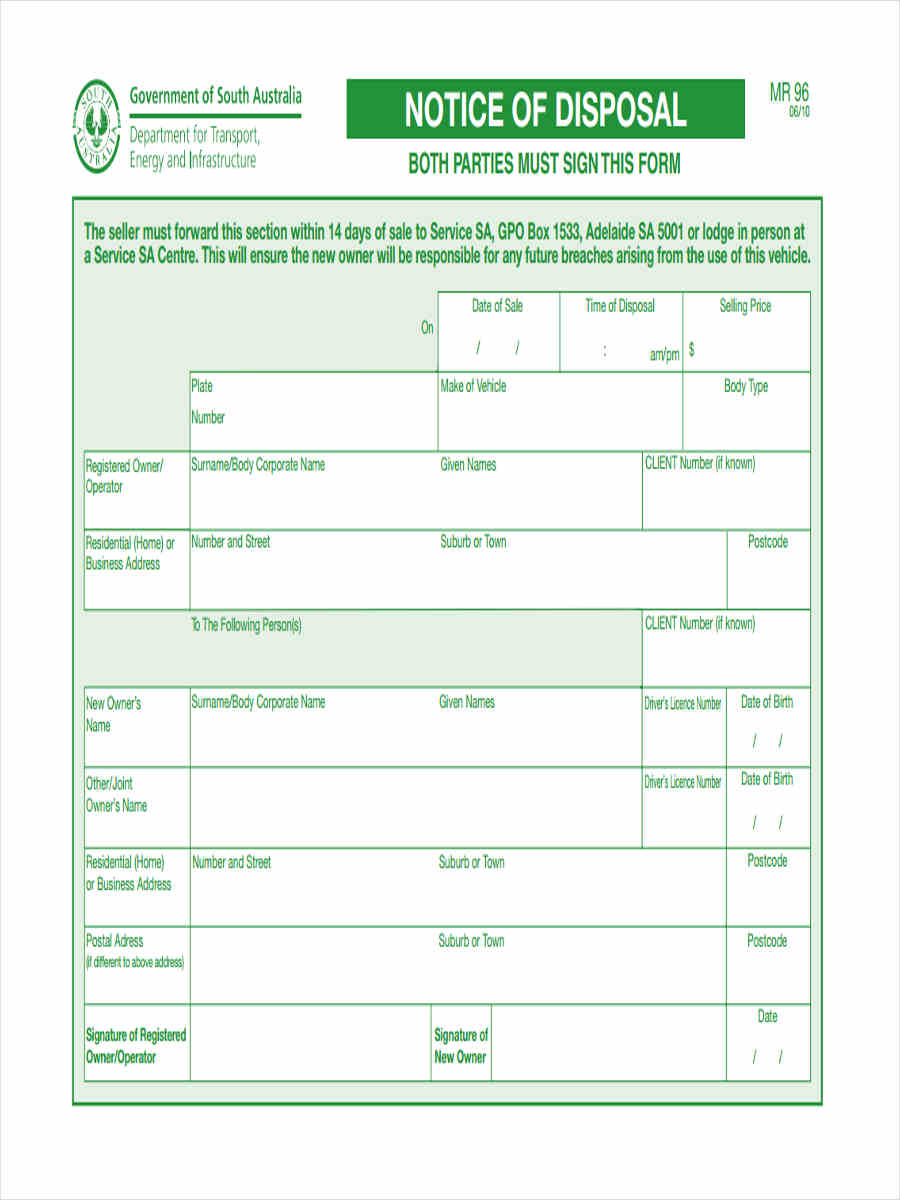
A destruction certificate, often referred to as a certificate of destruction, is a formal document issued to certify that specific items, assets, or data have been permanently and irretrievably destroyed or disposed of in accordance with predetermined standards and regulations. It acts as official proof, detailing what was destroyed, when it was destroyed, how it was destroyed, and by whom. This document is crucial for organizations that handle sensitive or confidential information, as well as those managing physical assets that require documented disposal.

The primary purpose of this certificate is to provide an auditable record of destruction, safeguarding the organization against potential liabilities related to data breaches, environmental non-compliance, or improper asset disposal. It transitions the responsibility for the destroyed items or data from the owner to the destruction service provider, or formally closes the loop if destruction is performed in-house.
Why a Destruction Certificate is Essential for Your Organization
In an era defined by data privacy regulations and heightened security concerns, the importance of a destruction certificate cannot be overstated. It offers a multitude of benefits that are critical for operational integrity, legal compliance, and reputation management.

Ensuring Legal and Regulatory Compliance
Many industries are subject to strict data protection and privacy laws, such as GDPR (General Data Protection Regulation), HIPAA (Health Insurance Portability and Accountability Act), PCI DSS (Payment Card Industry Data Security Standard), and SOX (Sarbanes-Oxley Act). These regulations often mandate the secure destruction of sensitive information and require organizations to demonstrate due diligence in their data lifecycle management. A destruction certificate serves as concrete evidence that these mandates have been met, providing an essential component of your compliance framework.
Protecting Against Data Breaches and Liability
The improper disposal of data is a leading cause of data breaches. If confidential information falls into the wrong hands due to inadequate destruction methods, the originating organization can face severe penalties, costly lawsuits, and irreparable damage to its brand. A destruction certificate minimizes this risk by providing official documentation that items containing sensitive data have been securely rendered unusable, thus limiting liability.

Creating an Indispensable Audit Trail
For internal and external audits, having a clear, concise, and complete record of destruction activities is paramount. Auditors will often request proof of secure disposal for various types of assets or data. A comprehensive destruction certificate template ensures that all necessary information is captured, providing an easily accessible and verifiable audit trail that demonstrates responsible data and asset management practices.
Supporting Environmental Responsibility
Beyond data, organizations often destroy physical assets, electronic waste (e-waste), or products that no longer meet quality standards. Many regulations govern the environmentally sound disposal of these materials. A destruction certificate can also document that assets have been destroyed and recycled responsibly, aligning with corporate social responsibility initiatives and environmental regulations.

Managing Asset Lifecycle and Inventory
For physical assets, a destruction certificate helps in accurately updating asset registries and inventory records. It provides the official record needed to remove assets from the books, preventing discrepancies and ensuring accurate financial reporting and asset management practices. This is particularly important for high-value equipment or controlled items.
Key Elements of a Comprehensive Destruction Certificate Template
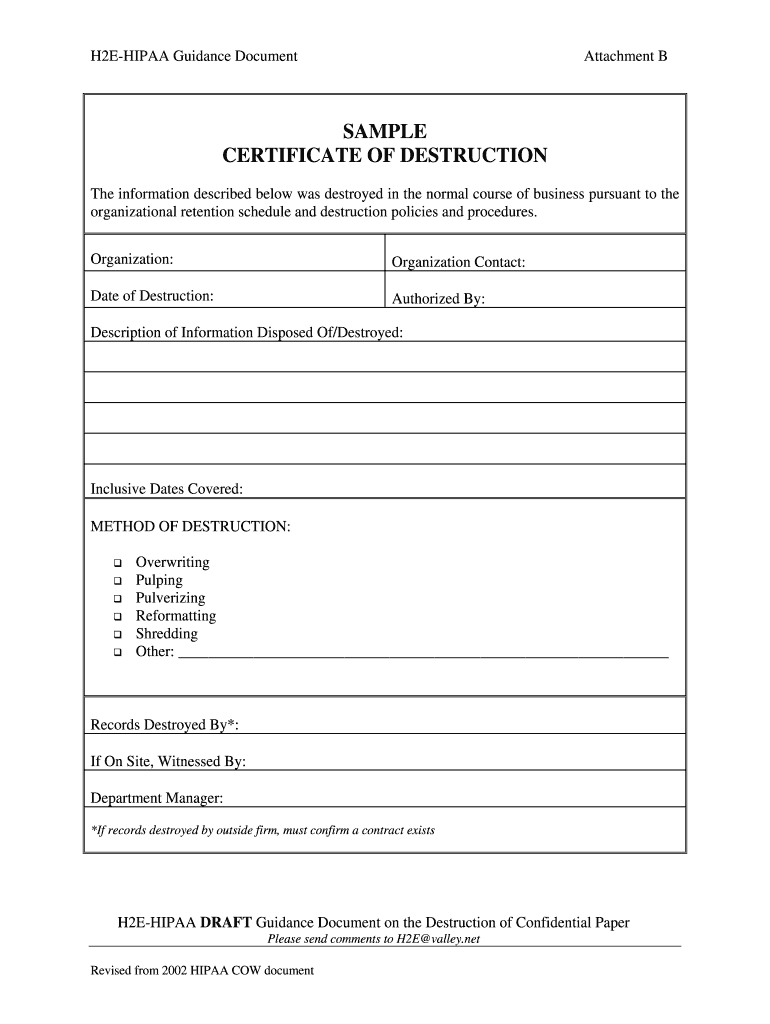
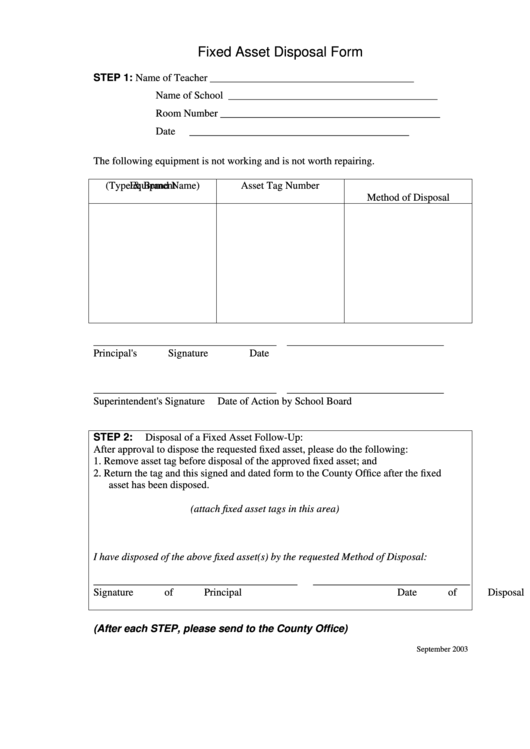
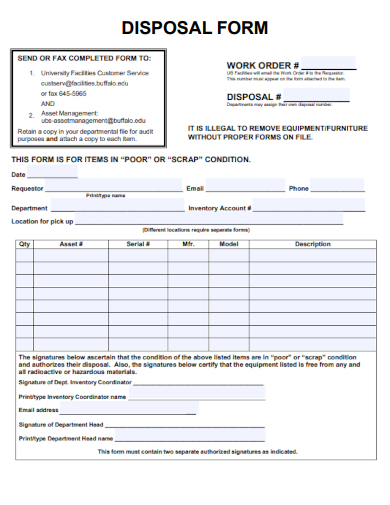
An effective Destruction Certificate Template must include specific fields and information to ensure its validity, comprehensiveness, and utility as a legal and auditable document. Omitting critical details can undermine its purpose and leave gaps in your compliance efforts.

Essential Information to Include:
- Unique Certificate ID/Reference Number: A unique identifier for tracking and referencing.
- Date of Issuance: The date the certificate was generated.
- Organization Requesting Destruction: Full name, address, and contact information of the entity requiring the destruction service.
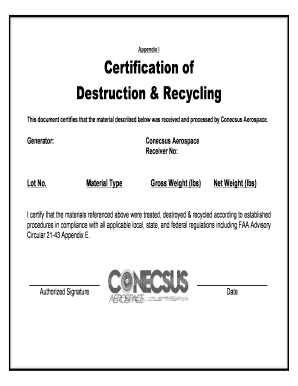
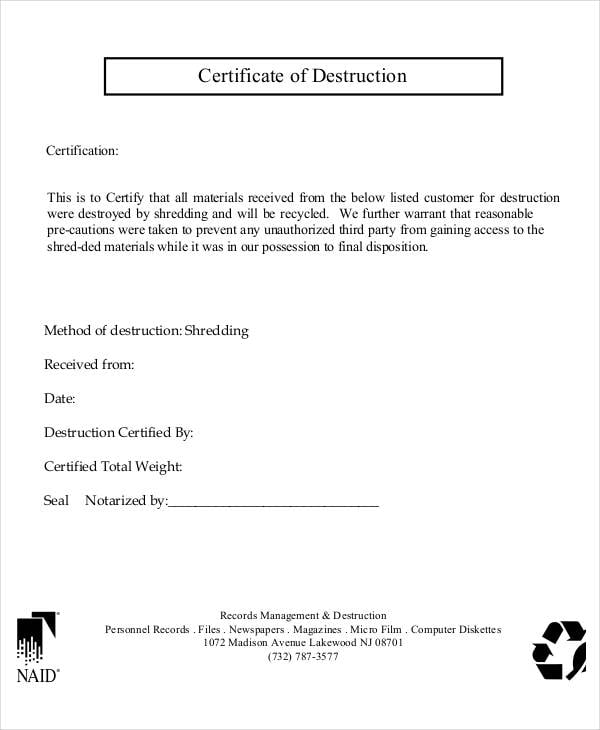
- Destruction Service Provider: Name, address, contact information, and any relevant certifications (e.g., NAID AAA Certification for data destruction) of the company performing the destruction.
- Date and Time of Destruction: The precise date(s) and time(s) when the destruction occurred.
- Location of Destruction: Where the destruction took place (e.g., on-site, off-site facility address).
- Description of Items Destroyed: A detailed list or description of the items, documents, or data storage devices that were destroyed. This might include:
- Type of item (e.g., hard drives, paper documents, product prototypes).
- Quantity (e.g., 50 hard drives, 10 boxes of documents).
- Serial numbers, asset tags, or specific identifying marks for each item.
- Capacity for data storage devices (e.g., 1TB HDD, 256GB SSD).
- Any other relevant identifiers that uniquely describe the destroyed material.
- Method of Destruction: A clear description of the process used for destruction (e.g., shredding, pulverization, incineration, degaussing, wiping to NIST 800-88 standards). Specific standards or equipment used should be noted.
- Witnesses (if applicable): Names and signatures of any individuals who observed the destruction process (e.g., client representatives, security personnel).
- Certification Statement: A formal statement affirming that the destruction was completed according to specified standards and that the items are irretrievably destroyed.
- Signature of Authorized Representative: Signature, printed name, title, and date from an authorized representative of the destruction service provider, certifying the completion of the destruction.
- Company Seal/Stamp: Official company seal or stamp for added authenticity.
By ensuring these components are consistently included, a Destruction Certificate Template provides a robust and defensible record of disposal activities.

Who Benefits from a Destruction Certificate Template?
Virtually any entity that handles sensitive information or manages physical assets can benefit from a standardized Destruction Certificate Template. The need for secure disposal and verifiable documentation is widespread across various sectors.
Businesses and Corporations
All businesses, regardless of size, generate and store confidential information, from employee records and financial statements to proprietary intellectual property. A template ensures consistent documentation when these materials are disposed of, protecting against legal issues and data breaches.
Healthcare Providers
Hospitals, clinics, and medical practices handle Protected Health Information (PHI) subject to stringent regulations like HIPAA. Documenting the destruction of patient records, medical images, and digital data is paramount for compliance and patient privacy.
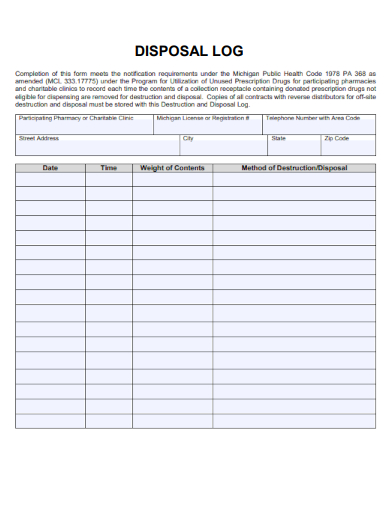
Financial Institutions
Banks, credit unions, and investment firms deal with vast amounts of sensitive customer financial data. Secure destruction of old account statements, loan applications, and data storage media is critical for compliance with regulations like PCI DSS and GLBA.
Government Agencies
Federal, state, and local government bodies manage sensitive citizen data, classified documents, and critical infrastructure information. They require rigorous documentation for the disposal of such materials to maintain national security and public trust.
Educational Institutions
Schools, colleges, and universities handle student records, faculty information, and research data. A template aids in the secure and compliant destruction of these records once their retention period expires.

IT and Data Centers
Companies that manage large volumes of digital data, including cloud service providers and data centers, frequently decommission old servers, hard drives, and other storage media. Documented destruction is essential to prevent data leakage.
Manufacturing and Retail
Businesses in these sectors may need to destroy defective products, expired goods, prototypes, or sensitive design specifications to protect brand integrity, prevent market contamination, or safeguard intellectual property.
How to Effectively Utilize Your Free Destruction Certificate Template
Having access to a Destruction Certificate Template is just the first step; knowing how to properly fill it out, customize it, and integrate it into your operational workflow is crucial for maximizing its benefits.
Step-by-Step Guide to Using the Template:
- Download and Review: Obtain a reputable free destruction certificate template. Thoroughly review its sections to understand what information is required.
- Customize for Your Needs:
- Branding: Add your company logo, contact information, and any specific branding elements.
- Specific Regulations: If you operate under specific regulatory frameworks (e.g., HIPAA, GDPR), ensure the template implicitly or explicitly covers requirements related to proof of destruction. You may need to add a clause referencing these standards.
- Types of Destruction: Tailor sections to fit the specific type of destruction (e.g., data, documents, physical assets). You might need different versions for different purposes or ensure a flexible "Description of Items" section.
- Gather Necessary Information: Before destruction occurs, collect all pertinent details:
- Identifiable information of the items to be destroyed (serial numbers, asset tags, item counts).
- Details of the destruction method planned.
- Information about the destruction service provider, if external.
- Complete the Template Accurately: Fill in all fields with precise and verifiable information. Accuracy is paramount for legal and audit purposes. Double-check serial numbers, quantities, and dates.
- Obtain Necessary Signatures: Ensure that all required parties, particularly the authorized representative of the destruction service provider (or your internal authorized personnel), sign and date the certificate. Witnesses, if present, should also sign.
- Secure Storage and Retention: Once completed and signed, store the certificate securely.
- Digital Copies: Create a digital copy (PDF) and store it in a designated, secure digital archive.
- Physical Copies: Retain a physical copy in an organized filing system.
- Retention Policy: Adhere to your organization's data retention policy and any legal requirements for how long these certificates must be kept. Typically, these are long-term records.
- Integrate into Workflow: Establish a standard operating procedure (SOP) for when and how destruction certificates are to be used within your organization's asset management, IT, and compliance departments.
By following these steps, your organization can leverage a free Destruction Certificate Template to build a robust, auditable, and legally defensible process for disposing of sensitive materials and assets.
Legal and Compliance Considerations for Destruction Certificates
While a Destruction Certificate Template provides a strong foundation, understanding the broader legal and compliance landscape is crucial for its effective use. The validity and enforceability of the certificate rely heavily on adherence to relevant laws and industry best practices.
Data Protection Regulations
- GDPR (General Data Protection Regulation): Requires organizations handling personal data of EU citizens to ensure its secure deletion when it's no longer necessary. A destruction certificate helps demonstrate compliance with the "right to be forgotten" and data minimization principles.
- HIPAA (Health Insurance Portability and Accountability Act): Mandates specific safeguards for Protected Health Information (PHI). Destruction of medical records and data must meet HIPAA's security rules, and a certificate provides proof of due diligence.
- CCPA/CPRA (California Consumer Privacy Act/California Privacy Rights Act): Similar to GDPR, these acts grant California residents rights over their personal information, including the right to delete. Documented destruction supports compliance.
- PCI DSS (Payment Card Industry Data Security Standard): Applies to entities handling credit card information. It requires secure disposal of cardholder data when it's no longer needed.
Corporate Governance and Audit Requirements
- Sarbanes-Oxley Act (SOX): While not directly about data destruction, SOX emphasizes the accuracy of financial reporting and internal controls. Proper asset disposal and documentation contribute to overall financial integrity and audit readiness.
- ISO 27001: An international standard for information security management systems. Documented destruction processes and certificates are vital components of a robust ISMS.
- Internal Audit Trails: Beyond external regulations, organizations need destruction certificates for internal audits to prove compliance with internal policies, verify asset write-offs, and ensure data hygiene.
Environmental Regulations
- WEEE Directive (Waste Electrical and Electronic Equipment): Applicable in the EU, this directive regulates the disposal of e-waste. While a destruction certificate primarily covers data, it can also confirm the responsible physical destruction of the electronic device.
- Local Waste Disposal Laws: Many jurisdictions have specific rules for disposing of hazardous materials or certain types of waste. The certificate should confirm compliance with these local laws.
Vendor Due Diligence
If you outsource destruction services, ensure your chosen vendor is reputable, certified (e.g., NAID AAA Certification for data destruction), and contractually obligated to provide comprehensive destruction certificates. The certificate from a trusted third party lends significant weight to your compliance efforts. Always verify their destruction methods and chain of custody procedures.
By staying informed about these legal and compliance considerations, organizations can ensure that their use of a Destruction Certificate Template is not merely a formality but a robust component of their risk management and governance strategy.
Conclusion
In a world increasingly reliant on data and stringent about privacy, the secure and documented destruction of sensitive information and assets is a non-negotiable aspect of responsible business practice. A Destruction Certificate Template emerges as an indispensable tool, providing a standardized, verifiable, and legally defensible record of these critical activities. It is far more than just a piece of paper; it is a shield against data breaches, a testament to regulatory compliance, and a vital component of a comprehensive audit trail.
From ensuring adherence to regulations like GDPR and HIPAA to safeguarding corporate reputation and managing asset lifecycles, the benefits of utilizing a well-structured destruction certificate are profound. By detailing what was destroyed, when, how, and by whom, it transforms a potentially risky process into a transparent and accountable operation. Leveraging a free, customizable template not only saves time and resources but also promotes consistency and professionalism in your disposal protocols. By understanding its key elements, recognizing who benefits, and integrating it effectively into your operational workflow, organizations can confidently navigate the complexities of secure destruction, fortifying their security posture, and demonstrating unwavering commitment to data privacy and regulatory compliance.
0 Response to "Destruction Certificate Template Free Download"
Posting Komentar